The knownhostsfile setting can be set during rclone config as an advanced. It has been found that this helps with IBM Sterling SFTP servers which have. Termius Corporation Termius - SSH/SFTP and Telnet client 5.2.1. This APK is signed by Termius Corporation and upgrades your existing app.
If you're anything like me, you probably log in and out of a half dozen remote servers (or these days, local virtual machines) on a daily basis. And if you're even more like me, you have trouble remembering all of the various usernames, remote addresses and command line options for things like specifying a non-standard connection port or forwarding local ports to the remote machine.
Shell Aliases
Let's say that you have a remote server named dev.example.com, which has not been set up with public/private keys for password-less logins. The username to the remote account is fooey, and to reduce the number of scripted login attempts, you've decided to change the default SSH port to 2200 from the normal default of 22. This means that a typical command would look like:
$ ssh fooey@dev.example.com -p 22000
password: *************
Not too bad.
We can make things simpler and more secure by using a public/private key pair; I highly recommend using ssh-copy-id for moving your public keys around. It will save you quite a few folder/file permission headaches.
$ ssh fooey@dev.example.com -p 22000
# Assuming your keys are properly setup…
Now this doesn't seem all that bad. To cut down on the verbosity you could create a simple alias in your shell as well:
$ alias dev='ssh fooey@dev.example.com -p 22000'
$ dev # To connect
This works surprisingly well: Every new server you need to connect to, just add an alias to your .bashrc (or .zshrc if you hang with the cool kids), and voilà.
~/.ssh/config
However, there's a much more elegant and flexible solution to this problem. Enter the SSH config file:
# contents of $HOME/.ssh/config
Host dev
HostName dev.example.com
Port 22000
User fooey
This means that I can simply $ ssh dev, and the options will be read from the configuration file. Easy peasy. Let's see what else we can do with just a few simple configuration directives.
Personally, I use quite a few public/private keypairs for the various servers and services that I use, to ensure that in the event of having one of my keys compromised the damage is as restricted as possible. For example, I have a key that I use uniquely for my Github account. Let's set it up so that that particular private key is used for all my github-related operations:
Host dev
HostName dev.example.com
Port 22000
User fooey
Host github.com
IdentityFile ~/.ssh/github.key
The use of IdentityFile allows me to specify exactly which private key I wish to use for authentification with the given host. You can, of course, simply specify this as a command line option for 'normal' connections:
$ ssh -i ~/.ssh/blah.key username@host.com
but the use of a config file with IdentityFile is pretty much your only option if you want to specify which identity to use for any git commands. This also opens up the very interesting concept of further segmenting your github keys on something like a per-project or per-organization basis:
Host github-project1
User git
HostName github.com
IdentityFile ~/.ssh/github.project1.key
Host github-org
User git
HostName github.com
IdentityFile ~/.ssh/github.org.key
Host github.com
User git
IdentityFile ~/.ssh/github.key
Which means that if I want to clone a repository using my organization credentials, I would use the following:
$ git clone git@github-org:orgname/some_repository.git
Going further
As any security-conscious developer would do, I set up firewalls on all of my servers and make them as restrictive as possible; in many cases, this means that the only ports that I leave open are 80/443 (for webservers), and port 22 for SSH (or whatever I might have remapped it to for obfuscation purposes). On the surface, this seems to prevent me from using things like a desktop MySQL GUI client, which expect port 3306 to be open and accessible on the remote server in question. The informed reader will note, however, that a simple local port forward can save you:
$ ssh -f -N -L 9906:127.0.0.1:3306 coolio@database.example.com
# -f puts ssh in background
Sftp Ssh Setup
# -N makes it not execute a remote command
This will forward all local port 9906 traffic to port 3306 on the remote database.example.com server, letting me point my desktop GUI to localhost (127.0.0.1:9906) and have it behave exactly as if I had exposed port 3306 on the remote server and connected directly to it.
Now I don't know about you, but remembering that sequence of flags and options for SSH can be a complete pain. Luckily, our config file can help alleviate that:
Host tunnel
HostName database.example.com
IdentityFile ~/.ssh/coolio.example.key
LocalForward 9906 127.0.0.1:3306
User coolio
Which means I can simply do:
$ ssh -f -N tunnel
And my local port forwarding will be enabled using all of the configuration directives I set up for the tunnel host. Slick.
Homework
There are quite a few configuration options that you can specify in ~/.ssh/config, and I highly suggest consulting the online documentation or the ssh_config man page. Some interesting/useful things that you can do include: change the default number of connection attempts, specify local environment variables to be passed to the remote server upon connection, and even the use of * and ? wildcards for matching hosts.
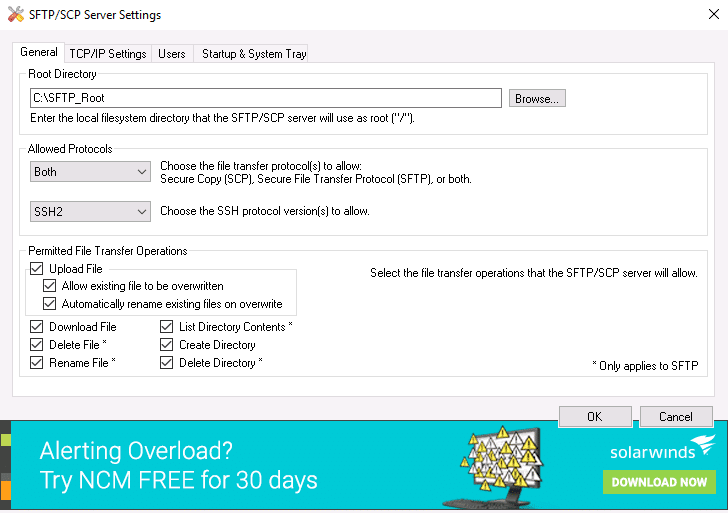
Ssh Sftp Server
I hope that some of this is useful to a few of you. Leave a note in the comments if you have any cool tricks for the SSH config file; I'm always on the lookout for fun hacks.
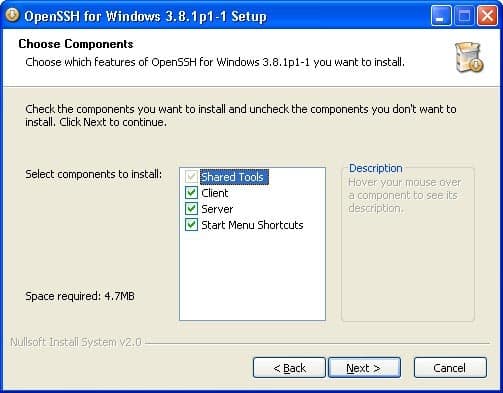
Recently, Microsoft has released a port of OpenSSH for Windows. You can use the package to set up an SFTP/SSH server on Windows.
- Installing SFTP/SSH Server
- Connecting to the server
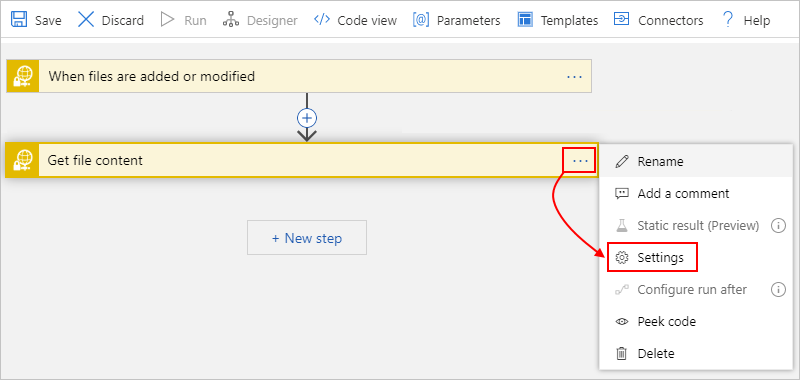
Advertisement
- In Settings app, go to Apps > Apps & features > Manage optional features.
- Locate “OpenSSH server” feature, expand it, and select Install.
Binaries are installed to %WINDIR%System32OpenSSH. Configuration file (sshd_config) and host keys are installed to %ProgramData%ssh (only after the server is started for the first time).
You may still want to use the following manual installation if you want to install a newer version of OpenSSH than the one built into Windows 10.
- Download the latest OpenSSH for Windows binaries (package
OpenSSH-Win64.ziporOpenSSH-Win32.zip) - As the Administrator, extract the package to
C:Program FilesOpenSSH - As the Administrator, install sshd and ssh-agent services:
- Allow incoming connections to SSH server in Windows Firewall:
- When installed as an optional feature, the firewall rule “OpenSSH SSH Server (sshd)” should have been created automatically. If not, proceed to create and enable the rule as follows.
- Either run the following PowerShell command as the Administrator:
ReplaceC:System32OpenSSHsshd.exewith the actual path to thesshd.exe(C:Program FilesOpenSSHssh.exe, had you followed the manual installation instructions above). - or go to Control Panel > System and Security > Windows Defender Firewall1 > Advanced Settings > Inbound Rules and add a new rule for port 22.
- Start the service and/or configure automatic start:
- Go to Control Panel > System and Security > Administrative Tools and open Services. Locate OpenSSH SSH Server service.
- If you want the server to start automatically when your machine is started: Go to Action > Properties. In the Properties dialog, change Startup type to Automatic and confirm.
- Start the OpenSSH SSH Server service by clicking the Start the service.
These instructions are partially based on the official deployment instructions.
Follow a generic guide for Setting up SSH public key authentication in *nix OpenSSH server, with the following difference:
- Create the
.sshfolder (for theauthorized_keysfile) in your Windows account profile folder (typically inC:Usersusername.ssh).2 - For permissions to the
.sshfolder and theauthorized_keysfile, what matters are Windows ACL permissions, not simple *nix permissions. Set the ACL so that the respective Windows account is the owner of the folder and the file and is the only account that has a write access to them. The account that runs OpenSSH SSH Server service (typicallySYSTEMorsshd) needs to have read access to the file. - Though, with the default Win32-OpenSSH configuration there is an exception set in
sshd_configfor accounts inAdministratorsgroup. For these, the server uses a different location for the authorized keys file:%ALLUSERSPROFILE%sshadministrators_authorized_keys(i.e. typicallyC:ProgramDatasshadministrators_authorized_keys).
Before the first connection, find out the fingerprint of the server’s host key by using ssh-keygen.exe for each file.
In Windows command-prompt, use:
Replace %WINDIR%System32 with %ProgramFiles%, if appropriate.
In PowerShell, use:
Replace $env:WINDIRSystem32 with $env:ProgramFiles, if appropriate.
You will get an output like this:
Start WinSCP. Login dialog will appear. On the dialog:
- Make sure New site node is selected.
- On New site node, make sure the SFTP protocol is selected.
- Enter your machine/server IP address (or a hostname) into the Host name box.
- Enter your Windows account name to the User name box. It might have to be entered in the format
user@domainif running on a domain. - For a public key authentication:
- Press the Advanced button to open Advanced site settings dialog and go to SSH > Authentication page.
- In Private key file box select your private key file.
- Submit Advanced site settings dialog with the OK button.
- For a password authentication:
- Enter your Windows account password to the Password box.
- If your Windows account does not have a password, you cannot authenticate with the password authentication (i.e. with an empty password), you need to use the public key authentication.
- Save your site settings using the Save button.
- Login using Login button.
- Verify the host key by comparing fingerprints with those collected before (see above).
Advertisement
Sftp Server Config
If you cannot authenticate to the server and use Windows 10 Developer mode, make sure that your OpenSSH server does not conflict with an internal SSH server used by the Developer mode. You may need to turn off the SSH Server Broker and SSH Server Proxy Windows services. Or run your OpenSSH server on a different port than 22.
- Guide to Installing Secure FTP Server on Windows using IIS;
- Guide to uploading files to SFTP server;
- Guide to automating operations (including upload).
- Windows Firewall on older versions of Windows.Back
- Windows File Explorer does not allow you to create a folder starting with a dot directly. As a workaround, use
.ssh., the trailing dot will allow you to bypass the restriction, but will not be included in the name.Back
